Busting three myths thwarting the IoT.
Cutting through the hype created by monstrous marketing budgets is key to demonstrating the real-world applications of a transformative technology.
Published 26/01/19
Like so many technologies before it, the IoT has fallen victim to the spreading of misinformation, unnecessarily exacerbating the complexity of a technology which maintains simplicity as one of its core values. The IoT is about connecting everything around us to gain insights into how we can improve the efficiency of our cities, the productivity of our factories and the safety of our transport systems.
The net for applications and use cases is cast incredibly wide, and this is perhaps the reason why the industry has tripped over itself in the realms of fragmentation and security. Make no mistake, mass adoption, in which billions of devices communicate with one another, is imminent. Our task now is to shape the growth of the IoT in a way that ensures privacy and security are not compromised, and that the tools we create evade the attention of those with ill-intent.
You see, an ecosystem of such great magnitude is composed of several layers, from the cloud back-end to the very devices beaming data through the air. It takes a minor failure in one, just one, of those layers for a pervasive outage to wreak havoc on the components further down, and even, upstream. It is for this reason that understanding what the IoT actually is, how it works and the use cases popping up is so vitally important as we enter the hyper-connected era.
The net for applications and use cases is cast incredibly wide, and this is perhaps the reason why the industry has tripped over itself in the realms of fragmentation and security. Make no mistake, mass adoption, in which billions of devices communicate with one another, is imminent. Our task now is to shape the growth of the IoT in a way that ensures privacy and security are not compromised, and that the tools we create evade the attention of those with ill-intent.
You see, an ecosystem of such great magnitude is composed of several layers, from the cloud back-end to the very devices beaming data through the air. It takes a minor failure in one, just one, of those layers for a pervasive outage to wreak havoc on the components further down, and even, upstream. It is for this reason that understanding what the IoT actually is, how it works and the use cases popping up is so vitally important as we enter the hyper-connected era.
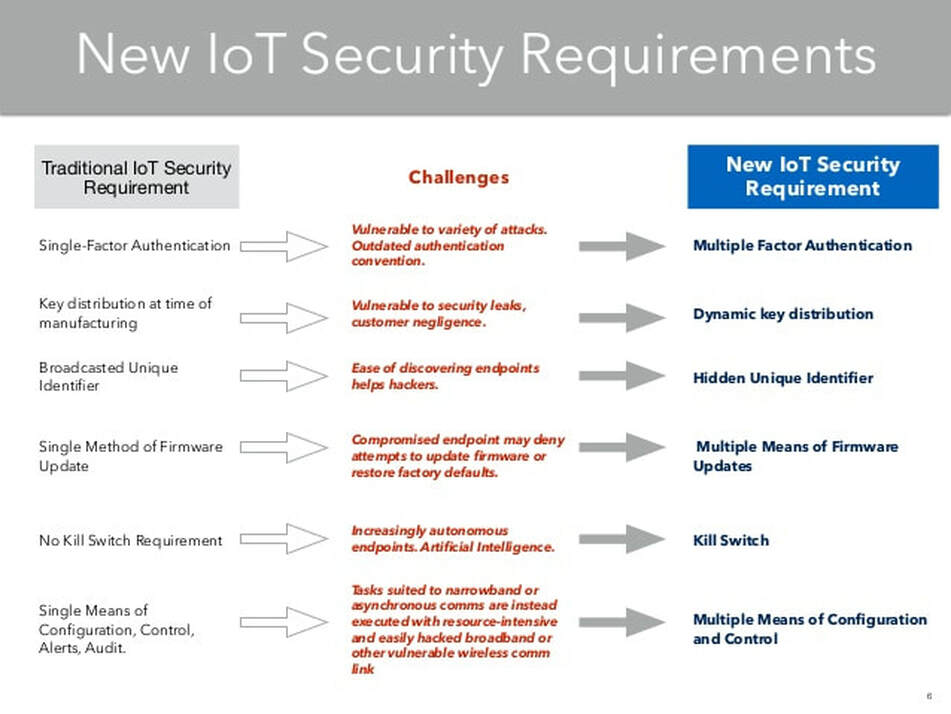
Security is an issue, a foundational one.
Let's get this straight out of the way, security is a basic but foundational element of the IoT, and without it, developing the technology would be futile. As we connect more devices to the Internet, we are inadvertently opening the floodgates to more pervasive cyber-attacks which threaten to compromise critical infrastructure that our societies depend on - for survival.
Today, in a connected world, we are actively engaged in a never-ending game of whack a mole, and the IoT makes that game insurmountable if security is not by-design within every layer of the vast IoT ecosystem.
There are various cross-enterprise security initiatives active for the IoT, with companies such as Google, Microsoft and Vodafone working to raise awareness about vulnerabilities, and working to make it easier for those vulnerabilities to be patched before they are exploited. For example, BitLocker and Secure Boot are now intrinsic features of the Windows IoT platform which encompasses popular IoT development kits such as Raspberry Pi.
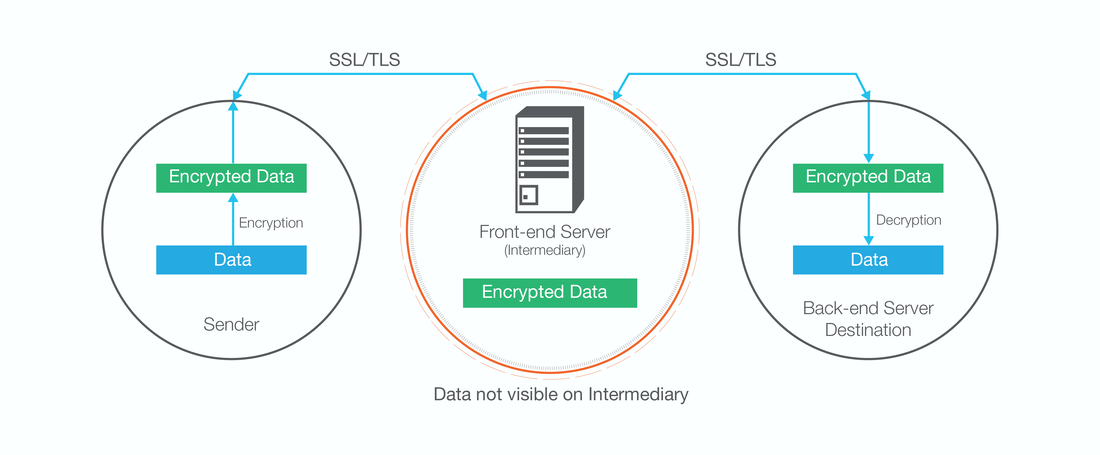
Of course, the integrity of LPWANs plays an instrumental role in the wider IoT environment as these networks act as a common ground for communication between millions of sensors and the cloud. Robust encryption is necessary on both the access and core network for data to remain secure.
Today, in a connected world, we are actively engaged in a never-ending game of whack a mole, and the IoT makes that game insurmountable if security is not by-design within every layer of the vast IoT ecosystem.
There are various cross-enterprise security initiatives active for the IoT, with companies such as Google, Microsoft and Vodafone working to raise awareness about vulnerabilities, and working to make it easier for those vulnerabilities to be patched before they are exploited. For example, BitLocker and Secure Boot are now intrinsic features of the Windows IoT platform which encompasses popular IoT development kits such as Raspberry Pi.
Of course, the integrity of LPWANs plays an instrumental role in the wider IoT environment as these networks act as a common ground for communication between millions of sensors and the cloud. Robust encryption is necessary on both the access and core network for data to remain secure.
In the case of Sigfox, the most ubiquitous IoT standard available today, base stations are connected to the Sigfox Cloud through a point to point link which is composed of a VPN and SSL encryption. To access the data stored on virtualised private servers, IT platforms such as those provided by Irish-born company Wia connect to the Sigfox Cloud via HTTPS-secured web interfaces.
Being the largest telecoms company in the world by revenue, Vodafone Group has pushed the IoT forward through its adoption and deployment of NB-IoT, a cellular-based LPWAN standard devised by 3GPP. The company is a prominent founder and member of the Internet of Things Security Foundation, an organisation which will work to enhance IoT security across the world through raising awareness about security vulnerabilities in connected devices, networks and protocols.
Delving deeper into the issue of NB-IoT security, a secret key built into physical SIMs at the point of manufacture is used to authenticate the network and the device, and to generate session keys which are frequently updated for encrypting traffic between the device and deep within the core network.
Being the largest telecoms company in the world by revenue, Vodafone Group has pushed the IoT forward through its adoption and deployment of NB-IoT, a cellular-based LPWAN standard devised by 3GPP. The company is a prominent founder and member of the Internet of Things Security Foundation, an organisation which will work to enhance IoT security across the world through raising awareness about security vulnerabilities in connected devices, networks and protocols.
Delving deeper into the issue of NB-IoT security, a secret key built into physical SIMs at the point of manufacture is used to authenticate the network and the device, and to generate session keys which are frequently updated for encrypting traffic between the device and deep within the core network.
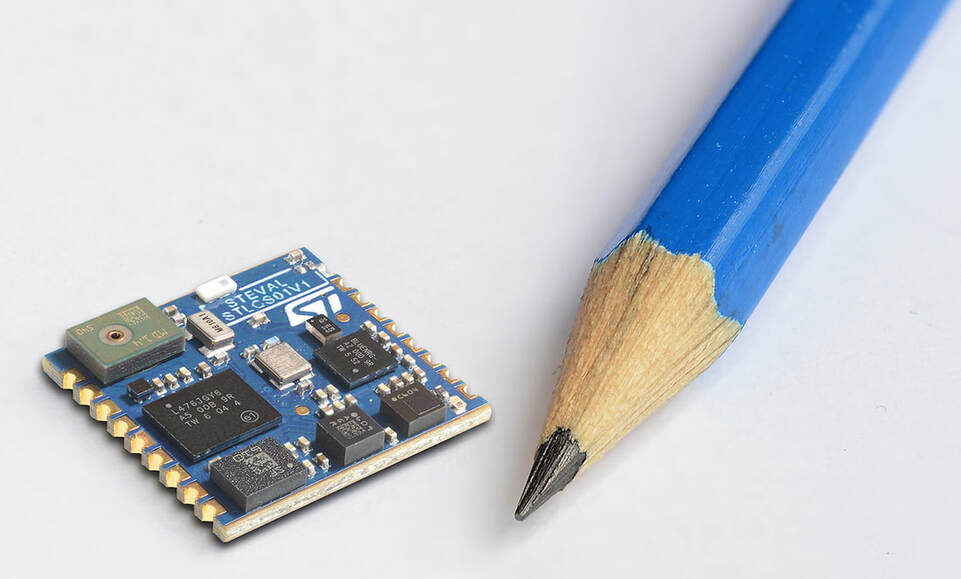
A factor which has hampered efforts to bolster the on-device security of connected sensors is cost and energy consumption. Many simple IoT sensors which cost less than €5 do not feature the required processing power to encrypt and decrypt traffic between the device and network. Moreover, duty cycle limitations such as those applying to Sigfox make it difficult for the authentication of a communication session as the number of bytes available is incredibly small.
A similar drawback mentioned above also applies to the challenges of delivering an OTA security update via a network with limited throughput. We need to reinvent the way in which such updates are distributed to millions of sensors multiple times a day. Dual-connectivity is a solution to this problem, pairing a high-throughput (and energy-sipping) technology such as WiFi with a low throughput alternative, think NB-IoT or Sigfox, in the radio modules of an IoT product.
A downlink message can be sent to a sensor via an LPWAN which instructs it to activate WiFi in anticipation of an OTA update. When this is complete, the WiFi function falls back into a state of sleep to conserve energy. There is also the possibility to break OTA updates into so-called 'parcels' which can be sent to the sensor at very specific times.
A similar drawback mentioned above also applies to the challenges of delivering an OTA security update via a network with limited throughput. We need to reinvent the way in which such updates are distributed to millions of sensors multiple times a day. Dual-connectivity is a solution to this problem, pairing a high-throughput (and energy-sipping) technology such as WiFi with a low throughput alternative, think NB-IoT or Sigfox, in the radio modules of an IoT product.
A downlink message can be sent to a sensor via an LPWAN which instructs it to activate WiFi in anticipation of an OTA update. When this is complete, the WiFi function falls back into a state of sleep to conserve energy. There is also the possibility to break OTA updates into so-called 'parcels' which can be sent to the sensor at very specific times.
The most divisive security concern with the IoT relates to the practice of storing and utilising personally-identifiable data such as health records. We need to think deeply about how much data companies should be allowed to collect, and what they can do with that data. Remember, data is the new oil, a valuable resource which is generated by us, the users of a service. Just to put this into context: would you be disturbed with the sharing of your health data to an insurance company who can, accordingly, tailor their prices and services towards you?
The IoT cannot advance in the absence of uncompromising security, this is a simple fact. And that security needs to run throughout the IoT ecosystem, from the tiny sensors deep within buildings to the base stations and servers that make up the access and core network. Encryption, open source code and cross-company collaboration will be key combatants to the exploitation of security vulnerabilities, ensuring the infrastructure and critical medical devices that we depend on keep functioning.
The IoT cannot advance in the absence of uncompromising security, this is a simple fact. And that security needs to run throughout the IoT ecosystem, from the tiny sensors deep within buildings to the base stations and servers that make up the access and core network. Encryption, open source code and cross-company collaboration will be key combatants to the exploitation of security vulnerabilities, ensuring the infrastructure and critical medical devices that we depend on keep functioning.
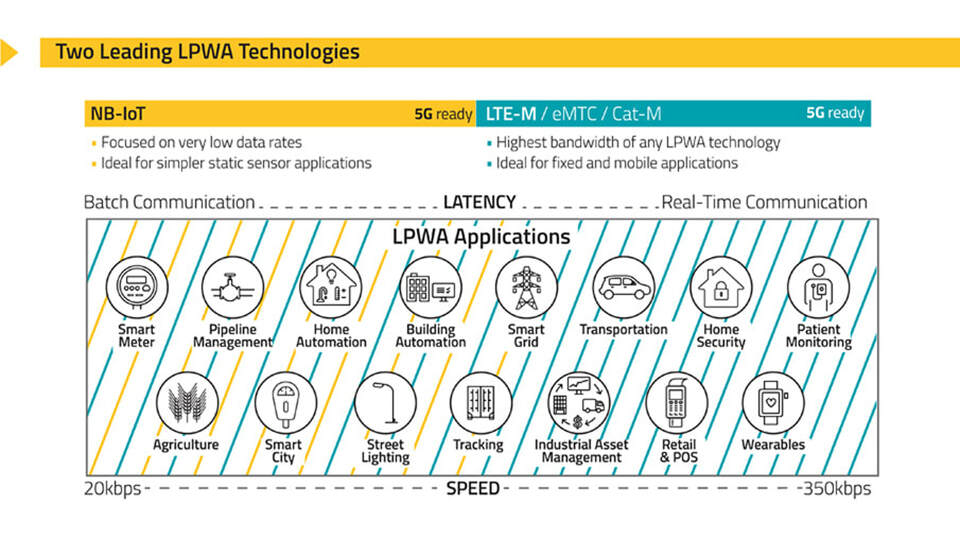
The IoT is not a one size fits all case.
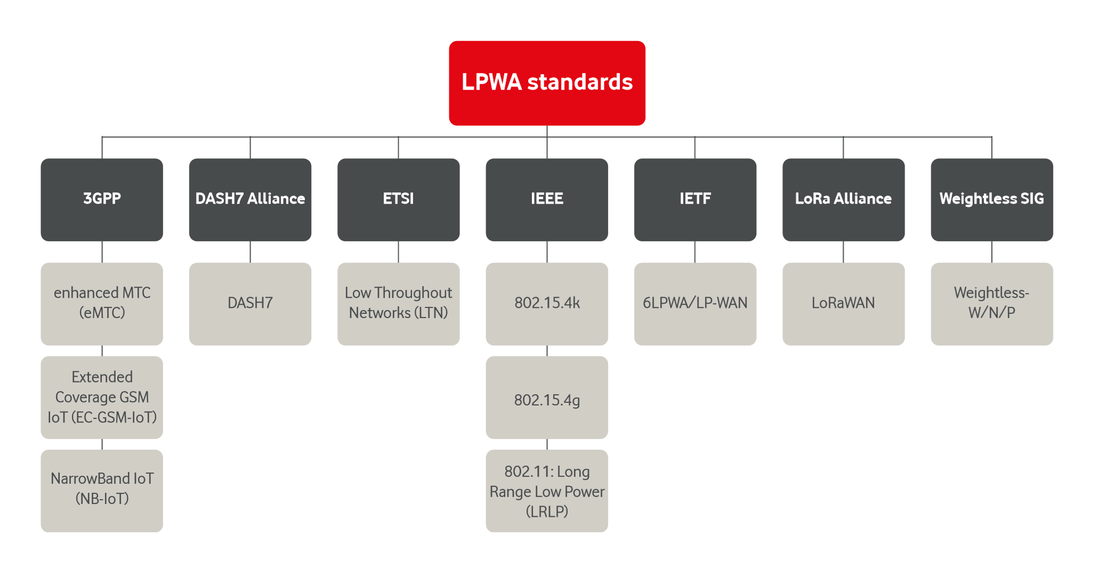
Every aspect of the IoT is diverse, and this is what renders the technology so adaptable. We need to move away from the consensus that one LPWAN standard is the most appropriate option for every intended use case. In fact, this couldn't be further from the truth.
There is a myriad of different sensors and devices which connect to the IoT. Some of these are simple, with very basic requirements. Think of a weather station which houses several sensors in a Stevenson Screen, each reporting their own metric about the state of the atmosphere at any one point of time. That metric could be temperature, it could be humidity or even the intensity of sunlight. However, all of these metrics can be sent to the cloud with minimal resources, paving the way for outstanding battery life in the range of multiple years. In this scenario, provided the frequency of communication is not an issue, Sigfox would be an excellent connectivity option: it's inexpensive, energy efficient and can work flawlessly in a 12-byte payload
There is a myriad of different sensors and devices which connect to the IoT. Some of these are simple, with very basic requirements. Think of a weather station which houses several sensors in a Stevenson Screen, each reporting their own metric about the state of the atmosphere at any one point of time. That metric could be temperature, it could be humidity or even the intensity of sunlight. However, all of these metrics can be sent to the cloud with minimal resources, paving the way for outstanding battery life in the range of multiple years. In this scenario, provided the frequency of communication is not an issue, Sigfox would be an excellent connectivity option: it's inexpensive, energy efficient and can work flawlessly in a 12-byte payload
Now think of an application for the IoT such as an autonomous vehicle or drone. The level of complexity rises exponentially compared to a temperature sensor, and so too do the connectivity requirements. For these use cases, a technology such as LTE Cat-4 is more suitable because it boasts greater bandwidth and reduced latency compared to both NB-IoT and Sigfox. These characteristics are essential for real-time communication, allowing cars to intelligently navigate around traffic collisions. For connected wearables and health sensors, LTE Cat-1 is the preferred solution, providing sufficient bandwidth and latency while reducing energy consumption compared to LTE Cat-4.
If a water utility company decides to install millions of sensors to collect data about the usage of its infrastructure, NB-IoT is a prime candidate thanks to its incredible underground and indoor signal penetration (164dB) ability and for the massive capacity that it can provide to the operator.
Choosing an LPWAN standard should be based upon the requirements of an individual sensor. Think about the desired lifespan, determined by its battery capacity and by the energy consumption of a particular networking technology. For example, the monitoring of electricity grids is not restricted to standards such as Sigfox because energy consumption is not an issue with mains-powered sensors.
If a water utility company decides to install millions of sensors to collect data about the usage of its infrastructure, NB-IoT is a prime candidate thanks to its incredible underground and indoor signal penetration (164dB) ability and for the massive capacity that it can provide to the operator.
Choosing an LPWAN standard should be based upon the requirements of an individual sensor. Think about the desired lifespan, determined by its battery capacity and by the energy consumption of a particular networking technology. For example, the monitoring of electricity grids is not restricted to standards such as Sigfox because energy consumption is not an issue with mains-powered sensors.
It is also vital to understand the required frequency of communication between the sensor and the cloud. Sigfox uses 200kHz of unlicensed spectrum in the 868-869MHz band in Europe, and the duty cycle limits this to six uplink messages per hour which have a twelve-byte payload and four downlink messages per hour which have a payload of eight bytes. In this way, Sigfox is not appropriate for a use case which demands real-time communication.
The nature of use cases for the IoT will also determine the level of security that is required. Applications which involve mission-critical infrastructure should utilise NB-IoT or LTE-M because of their bank-grade encryption standards and 4G LTE security standards. Technologies such as Sigfox and LoRa are inherently less secure because messages in transit are not encrypted by default and because unlicensed spectrum is more vulnerable to mal-use. Furthermore, the use of proprietary code makes it more difficult for the identification of security vulnerabilities in these technologies.
Finally, considering the desired downlink and uplink data rate, combined with latency, is important and can vary wildly with different use cases as explained. NB-IoT's superior downlink (0.5-200kbps) and uplink (0.3-180kbps) rates compared to Sigfox and LoRa make it more fitting for applications that are located at the cell edge where signal conditions are poor.
The nature of use cases for the IoT will also determine the level of security that is required. Applications which involve mission-critical infrastructure should utilise NB-IoT or LTE-M because of their bank-grade encryption standards and 4G LTE security standards. Technologies such as Sigfox and LoRa are inherently less secure because messages in transit are not encrypted by default and because unlicensed spectrum is more vulnerable to mal-use. Furthermore, the use of proprietary code makes it more difficult for the identification of security vulnerabilities in these technologies.
Finally, considering the desired downlink and uplink data rate, combined with latency, is important and can vary wildly with different use cases as explained. NB-IoT's superior downlink (0.5-200kbps) and uplink (0.3-180kbps) rates compared to Sigfox and LoRa make it more fitting for applications that are located at the cell edge where signal conditions are poor.
Gathering data without insight is futile.
It's staggering to learn of just how many businesses are adopting the IoT across the world, with the growth spanning across countless different industries. However, a fatal mistake which many people commit is the conception of an idea that the IoT merely concerns the deployment of sensors - nothing more.
The purpose of this technology is to gather data that can be used to provide valuable insights into the operation of an organisation or system. This insight can then be translated into action, in the form of implementing change to, for example, improve operational efficiency or to reduce industrial waste. Without the deep analysis and understanding of data, the IoT cannot become an asset to businesses, instead, it will be an expense.
This is is a major contributor to the reason why IoT companies are now becoming providers of comprehensive solutions. Simply developing and launching a product is not enough, there needs to be a full-fledged vertically integrated solution which allows businesses to interact with the data they are gathering from their sensors and to provide the necessary tools to open the gateway to the identification of trends, commonly referred to as "Big Data".
The purpose of this technology is to gather data that can be used to provide valuable insights into the operation of an organisation or system. This insight can then be translated into action, in the form of implementing change to, for example, improve operational efficiency or to reduce industrial waste. Without the deep analysis and understanding of data, the IoT cannot become an asset to businesses, instead, it will be an expense.
This is is a major contributor to the reason why IoT companies are now becoming providers of comprehensive solutions. Simply developing and launching a product is not enough, there needs to be a full-fledged vertically integrated solution which allows businesses to interact with the data they are gathering from their sensors and to provide the necessary tools to open the gateway to the identification of trends, commonly referred to as "Big Data".
Historically, it has been difficult for businesses to derive valuable insights from sensor data because of the absence of intuitive web interfaces. This is, however, changing thanks to the introduction of solutions from companies such as Wia, an Irish start-up that integrates IoT products with its cloud API for easy access to and augmentation of an IoT sensor. Without a doubt, these advancements are critical stepping stones for the IoT because they allow more businesses to benefit from the technology.
The growth of Big Data is a similarly important milestone, and it holds the potential to radically transform the way in which we think about the world. Aggregating colossal swathes of data can offer us new breakthroughs in the detection and treatment of diseases, and in the management of complex logistics operations.
To draw attention to how the IoT and Big Data can work together, we need to investigate some examples of this in the real world. Living within the logistics business of shipping, UPS has deployed sensors across its international operation to monitor speed, miles per gallon, mileage, the frequency of stops and engine health with the intention of using this data to reduce operational expenses, enhance efficiency and to decrease its impact on the environment. The deployment of sensors by UPS gathers over 200 points of data for each vehicle in a fleet exceeding 80,000 vehicles, every single day. This has helped the company to reduce the wastage of fuel, idle time and production of atmospheric pollutants.
The growth of Big Data is a similarly important milestone, and it holds the potential to radically transform the way in which we think about the world. Aggregating colossal swathes of data can offer us new breakthroughs in the detection and treatment of diseases, and in the management of complex logistics operations.
To draw attention to how the IoT and Big Data can work together, we need to investigate some examples of this in the real world. Living within the logistics business of shipping, UPS has deployed sensors across its international operation to monitor speed, miles per gallon, mileage, the frequency of stops and engine health with the intention of using this data to reduce operational expenses, enhance efficiency and to decrease its impact on the environment. The deployment of sensors by UPS gathers over 200 points of data for each vehicle in a fleet exceeding 80,000 vehicles, every single day. This has helped the company to reduce the wastage of fuel, idle time and production of atmospheric pollutants.
Building on the UPS example, Virgin Atlantic is applying the benefits of IoT and Big Data integration to the airline industry, a business where time is literally money. The company's fleet of Boeing-787 aircraft is fitted with dozens of connected sensors, most notably for cargo tracking. Incredibly, the IoT equipment on board the fleet can generate over a half a terabyte of data (500GB+) per flight. Processing such a large volume of data is not easy, but the results can be truly astounding. Virgin explains that Big Data is being used to predict maintenance requirements and to improve flight and fuel efficiency.
As we move closer towards a point when the IoT explodes exponentially, complex Big Data algorithms will necessitate unprecedented levels of processing power, and breakthroughs in GPU design and the miniaturisation of storage devices. It is forthcoming that these algorithms will have the capacity to deliver real-time analytics aggregated from billions of sensors across the world, and thereby solve problems that would appear impossible today.
As we move closer towards a point when the IoT explodes exponentially, complex Big Data algorithms will necessitate unprecedented levels of processing power, and breakthroughs in GPU design and the miniaturisation of storage devices. It is forthcoming that these algorithms will have the capacity to deliver real-time analytics aggregated from billions of sensors across the world, and thereby solve problems that would appear impossible today.
Conclusion: Blurring the divide.
Continued advancement in the IoT industry will blur the divide between the physical and digital worlds to a level that has never been accomplished before. Revolutionary, transformative and cutting edge are all terms that describe the IoT and its potential, with precise exactness.
However, this will not happen, period, if the entire industry doesn't wake up to the eerily dystopian-style security vulnerabilities, to the invasions of personal privacy and to the mess that is fragmentation and cross-platform interoperability. These are teething issues that need to be chiselled away, one by one, through the encouragement of industry collaboration and the development of standards-based technologies.
I, like so many others, know that such challenges will be tackled by creative thinkers and next-generation innovators, providing us with a technology that is fit for purpose. It's simply stunning to witness the IoT extending life expectancy rates in some countries by decades through the facilitation of medical breakthroughs and to understand the tremendous results of driving down fossil fuel usage. We are the ones at the wheel of the IoT, so just ask yourself, where do you want it to go?
However, this will not happen, period, if the entire industry doesn't wake up to the eerily dystopian-style security vulnerabilities, to the invasions of personal privacy and to the mess that is fragmentation and cross-platform interoperability. These are teething issues that need to be chiselled away, one by one, through the encouragement of industry collaboration and the development of standards-based technologies.
I, like so many others, know that such challenges will be tackled by creative thinkers and next-generation innovators, providing us with a technology that is fit for purpose. It's simply stunning to witness the IoT extending life expectancy rates in some countries by decades through the facilitation of medical breakthroughs and to understand the tremendous results of driving down fossil fuel usage. We are the ones at the wheel of the IoT, so just ask yourself, where do you want it to go?
Pest Pulse is using the IoT to tackle an old problem in a new wayTraversing the ups and downs of an IoT industry on the brink of explosion, Brian Monaghan explains where his company fits in.
|